Underwater wireless communication is the wireless communication in which acoustic signals carry digital information through an underwater channel.
Introduction to Underwater Wireless Communication Network
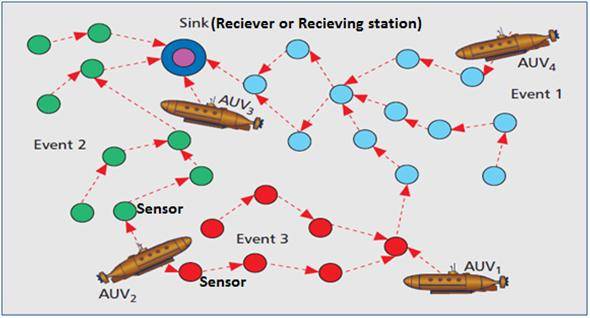
Securing Underwater Wireless Communication Networks (UWCNs) are constituted by sensors and Autonomous Underwater Vehicles (AUVs) that interact to perform specific applications such as underwater monitoring (Fig. 1). Coordination and sharing of information between sensors and AUVs make the provision of security challenging. The aquatic environment is particularly vulnerable to malicious attacks due to the high bit error rates, large and variable propagation delays, and low bandwidth of acoustic channels. Achieving reliable intervehicle and sensor-AUV communication is especially difficult due to the mobility of AUVs and the movement of sensors with water currents. The unique characteristics of the underwater acoustic channel, and the differences between underwater sensor networks and their ground based counterparts require the development of efficient and reliable security mechanisms. In this post, the possible attacks and countermeasures, research challenges related to secure time synchronization, localization, and routing will be discussed.
2. CHARACTERISTICS AND VULNERABILITIES OF UWCNs
Underwater sensor networks have some similarities with their ground-based counterparts such as their structure, function, computation and energy limitations. However, they also have differences, which can be summarized as follows.Radio waves do not propagate well underwater due to the high energy absorption of water.Therefore,underwater communications are based on acoustic links characterized by large propagation delays. The propagation speed of acoustic signals in water (typically 1500 m/s) is five orders of magnitude lower than the radio wave propagation speed in free space. Acoustic channels have low bandwidth. The link quality in underwater communication is severely affected by multipath, fading, and the refractive properties of the sound channel. As a result, the bit error rates of acoustic links are often high, and losses of connectivity arise. Underwater sensors move with water currents, and AUVs are mobile. Although certain nodes in underwater applications are anchored to the bottom of the ocean, other applications require sensors to be suspended at certain depths or to move freely in the underwater medium. The future development of geographical routing is very promising in UWCNs due to its scalability and limited signaling properties. However, it cannot rely on the Global Positioning System(GPS) because it uses radar waves in the 1.5 GHz band that do not propagate in water. Since underwater hardware is more expensive, underwater sensors are sparsely deployed.
Underwater communication systems have more stringent power requirements than terrestrial systems because acoustic communications are more power-hungry, and typical transmission distances in UWCNs are greater; hence, higher transmit power is required to ensure coverage. The above mentioned characteri-stics of UWCNs have several security implications.UWCNs suffer from the following vulnerabilities. High bit error rates cause packet errors.Consequently, critical security packets can be lost. Wireless underwater channels can be eavesdropped on. Attackers may intercept the informat-ion transmitted and attempt to modify or drop packets. Malicious nodes can create out-of-band connections via fast radio (above the water surface) and wired links, which are referred to as wormholes. Since sensors are mobile, their relative distances vary with time. The dyna-mic topology of the underwater sensor network not only facilitates the creation of wormholes but it also complicates their detection. Since power consumption in underwater communications is higher than in terrestrial radio communicate-ons and underwater sensors are sparsely deployed, energy exhaustion attacks to drain the batteries of nodes pose a serious threat for the network lifetime.
3. ATTACKS ON UWCNS AND COUNTERMEASURES
Both intervehicle and sensor-AUV communications can be affected by denial-of-service (DoS)attacks. Next, we summarize typical DoS attacks, evaluate their dangers, and indicate possible defenses to muffle their effects.
3.1 JAMMING
A jamming attack consists of interfering with the physical channel by putting up carriers on the frequencies neighbor nodes use to communicate.Since underwater acoustic frequency bands are narrow (from a few to hundreds of kilohertz), Securing underwater wireless communication networks are vulnerable to narrowband jamming. Localization is affected by the replay attack when the attacker jams the communication between a sender and a receiver, and later replays the same message with stale information (an incorrect reference) posing as the sender(Fig. 2).Since jamming is a common attack in wireless networks, some of the solutions proposed for traditional wireless networks can be applied.Spread spectrum is the most common defense against jamming. Frequency hopping spread spectrum (FHSS) and direct sequence spread spectrum (DSSS) in underwater communications are drawing attention for their good performance under noise and multipath interference. These schemes are resistant to interference from attackers, although not infallible. An attacker can jam a wide band of the spectrum or follow the precise hopping sequence when an FHSS scheme is used.
A high-power wideband jamming signal can be used to attack a DSSS scheme. Underwater sensors under a jamming attack should try to preserve their power. When jamming is continuous, sensors can switch to sleep mode and wake up periodically to check if the attack is over. When jamming is intermittent, sensors can buffer data packets and only send high-power high-priority messages to report the attack when a gap in jamming occurs.In ground-based sensor networks, other sensors located along the edge of the area under attack can detect the jamming signal as higher than-normal background noise and report intrusion to outside nodes. That will cause any further traffic to be rerouted around the jammed region. However, this solution cannot be applied to UWCNs, since nodes underwater are usually sparsely deployed, which means there would not be enough sensors to delimit the jammed region accurately and reroute traffic around it. Another solution proposed for ground-based sensor networks against jamming is to use alternative technologies for communication such as infrared or optical. However, this solution cannot be applied either, since optical and infrared waves are severely attenuated under water.

3.2 WORMHOLE ATTACK
A wormhole is an out-of-band connection created by the adversary between two physical locations in a network with lower delay and higher bandwidth than ordinary connections. This connection uses fast radio (above the sea surface) or wired links (Fig. 3) to significantly decrease the propagation delay. In a wormhole attack the malicious node transfers some selected packets received at one end of the wormhole to the other end using the out-of-band connection, and re-injects them into the network. The effect is that false neighbor relationships are created, because two nodes out of each others range can erroneously conclude that they are in proximity of one another due to the wormholes presence. This attack is devastating. Routing protocols choose routes that contain wormhole links because they appear to be shorter; thus, the adversary can monitor network traffic and delay or drop packets sent through the wormhole. Localization protocols can also be affected by these attacks when malicious nodes claim wrong locations and mislead other nodes.
One proposed method for wormhole detection in ground-based sensor networks consists of estimating the real physical distance between two nodes to check their neighbor relationship. If the measured distance is longer than the nodes communication range, it is assumed that the nodes are connected through a wormhole.However, accurate distance estimation depends on precise localization (geographical packet leashes, wormhole detection using position information of anchors), tight clock synchronization (temporal packet leashes), or use of specific hardware (directional antennas). In underwater communications accurate localization and time synchronization are still challenging. The authors propose a distributed mechanism named Distributed Visualization of Wormhole (Dis-VoW) to detect wormhole attacks in three-dimensional underwater sensor networks. In Dis-VoW, every sensor collects the distance estimations to its neighbors using the round-trip time of acoustic signals; after these distances are broadcast by each sensor to its neighbors, every node is able to construct the local network topology (virtual layout) within two hops using multidimensional scaling (MDS). Since a wormhole contracts the virtual layout at certain regions, some nodes far away appear to be neighbors, and these contradictions can be detected visualizing the virtual layout. A wormhole indicator variable is defined to compute the distortion in angles; the distortion in edge lengths is computed as the difference between the measured distances among neighboring sensors and the lengths of the reconstructed connections. In a suite of protocols is proposed to enable wormhole-resilient secure neighbor discovery with high probability in underwater sensor networks. This solution is based on the direction of arrival (DoA) estimation of acoustic signals, which depends on the relative locations of signal transmitters and receivers, and cannot be manipulated.

3.3 SINKHOLE ATTACK
In a sinkhole attack, a malicious node attempts to attract traffic from a particular area toward it; for example, the malicious node can announce a high-quality route. Geographic routing and authentication of nodes exchanging routing information are possible defenses against this ttack, but geographic routing is still an open research topic in UWCNs.
3.4 HELLO FLOOD ATTACK
A node receiving a HELLO packet from a malicious node may interpret that the adversary is a neighbor; this assumption is false if the adversary uses high power for transmission. Bidirectional link verification can help protect against this attack, although it is not accurate due to node mobility and the high propagation delays of UWCNs. Authentication is also a possible defense.
3.5 ACKNOWLEDGMENT SPOOFING
A malicious node overhearing packets sent to neighbor nodes can use this information to spoof link layer acknowledgments with the objective of reinforcing a weak link or a link located in a shadow zone. Shadow zones are formed when the acoustic rays are bent and sound waves cannot penetrate. They cause high bit error rates and loss of connectivity. This way, the routing scheme is manipulated. A solution to this attack would be encryption of all packets sent through the network.
3.6 SELECTIVE FORWARDING
Malicious nodes drop certain messages instead of forwarding them to hinder routing. In UWCNs it should be verified that a receiver is not getting the information due to this attack and not because it is located in a shadow zone.Multipath routing and authentication can be used to counter this attack, but multipath routing increases communication overhead.
3.7 SYBIL ATTACK
An attacker with multiple identities can pretend to be in many places at once. Geographic routing protocols are also misled because an adversary with multiple identities can claim to be in multiple places at once (Fig. 4).

Authentication and position verification are methods against this attack, although position verification in UWCNs is problematic due to mobility.
4. SECURITY REQUIREMENTS
In Securing underwater wireless communication networks the following security requirements should be considered.
4.1 AUTHENTICATION
Authentication is the proof that the data was sent by a legitimate sender. It is essential in military and safety-critical applications of UWCNs. Authentication and key establishment are strongly related because once two or more entities verify each others authenticity, they can establish one or more secret keys over the open acoustic channel to exchange information securely; conversely,an already established key can be used to perform authentication. Traditional solutions for key generation and update (renewal) algorithms should be adapted to better address the characteristics of the underwater channel. In, a key generation system is proposed that requires only a threshold detector, lightweight computation,and communication costs. It exploits reciprocity, deep fades (strong destructive interference),randomness extractor, and robust secure fuzzy information re-conciliators. This way, the key is generated using the characteristics of the underwater channel and is secure against adversaries who know the number of deep fades but not their locations.
4.2 CONFIDENTIALITY
Confidentiality means that information is not accessible to unauthorized third parties. Theref-ore, confidentiality in critical applications such as maritime surveillance (Fig. 5) should be guaranteed.

4.3 INTEGRITY
It ensures that information has not been altered by any adversary. Many underwater sensor applications for environmental preservation, such as water quality monitoring, rely on the integrity of information.
4.4 AVAILABILITY
The data should be available when needed by an authorized user. Lack of availability due to denial-of-service attacks would especially affect time-critical aquatic exploration applications such as prediction of seaquakes.
5. RESEARCH CHALLENGES
The security issues and open challenges for secure time synchronization, localization, and routing in Securing underwater wireless communication networks are summarized in the following sections.
5.1 SECURE TIME SYNCHRONIZATION
Time synchronization is essential in many underwater applications such as coordinated sensing tasks. Also, scheduling algorithms such as time division multiple access (TDMA) require precise timing between nodes to adjust their sleep-wakeup schedules for power saving. For example, in water quality monitoring, sensors are deployed at different depths because the chemical characteristics of water vary at each level.The design of a delay-tolerant time synchronization mechanism is very important to accurately locate the water contaminant source, set up the sleep-wakeup schedules among neighboring nodes appropriately, and log the water quality data correctly into the annual database with accurate timing information. Achieving precise time synchronization is especially difficult in underwater environments due to the characteristics of UWCNs. For this reason, the time synchronization mechanisms proposed for ground-based sensor networks cannot be applied, and new mechanisms have been proposed. Tri-Message is a time synchronization protocol designed for high-latency networks with a synchronization precision that increases with distance. A multilateration algorithm is proposed in for localization and synchronization in 3D underwater acoustic sensor networks. It is assumed that a set of anchors, several buoys on the ocean surface, already know their locations and time without error.
A group of nearby sensors receives synchronization packets containing the coordinates and packet transmit times from at least five anchor nodes and performs multilateration to obtain their own locations. The sensors learn the time difference between themselves and each anchor node by comparing their local times at which they received the time synchronization packet with the transmit time plus propagation delays; these nodes subsequently become new anchor nodes and thereafter broadcast new synchronization packets to a larger range, and so on. MU-Sync is a cluster-based synchronization protocol that estimates the clock skew by performing the linear regression twice over a set of local time information gathered through message exchanges. The first linear regression enables the cluster head to offset the effect of long and varying propagation delay; the second regression enables the clusterhead to obtain the final estimated skew and offset.None of the aforementioned time synchronization schemes consider security,although it is critical in the underwater environment.Time synchronization disruption due to masquerade, replay and message manipulation attacks, can be addressed using cryptographic techniques. However, countering other possible attacks such as delays (deliberate delaying the transmission of time synchronization messages) and DoS attacks requires the use of other strategies. The countermeasures against delay attacks proposed in for ground-based sensor networks are not applicable to UWCNs.They are based on the detection of outliers (malicious time offsets), but they do not distinguish between deliberate alterations and abnormal values resulting from long and variable propag-ation delays or node mobility. Moreover, they do not support global synchronization in multi-hop sensor networks.
A correlation-based security model for water quality monitoring systems has been proposed in to detect outlier timestamps due to insider attacks. The authors prove that the acoustic propagation delays between two sensors in neighboring depth levels fit an approximately normal distribution, which means that the timestamps between them should correlate. However, this correlation is lost if a captured inside node is sending falsified timestamps. With proper design of a timestamp sliding window scheme, insider attacks are detected. Each sensor should obtain timestamp readings from multiple sensors and calculate the correlation coefficient for each neighbors timestamp, obtaining a window of coefficients. If a coefficient of the window of data is below a threshold, it is an outlier value. If the abnormal percentage of data in one window (outlier percentage) is consistently (10 consecutive windows) higher than a predetermined threshold, the corresponding neighbor is flagged as a malicious node generating insider attacks. However, identifying a neighbor node as malicious is difficult, because sometimes timestamps can be corrupted due to propagation delay variations caused by the channel rather than deliberately. Because of wave motion, the signal multipath components undergo time-varying propagation delays. Node mobility due to water currents also modifies the propagation delays. In order to better distinguish between unintended and malicious timestamp alterations, the authors in improve the proposed scheme by using as a second step a statistical reputation and trust model to detect outlier timestamps, and identify nodes generating insider attacks. It is based on quantitative measurements and on the assumption that identifying an insider attacker requires long-term behavior observations. The following open research issues for secure time synchronization need to be addressed:
- Because of the high and variable propagation delays of UWCNs, the time required to synchronize nodes should be investigated.
- Efficient and secure time synchronization schemes with small computation and communications costs need to be designed to defend against delay and wormhole attacks.
5.2 SECURE LOCALIZATION
Localization is a very important issue for data tagging. Sensor tasks such as reporting the occurrence of an event or monitoring require localization information. Localization can also help in making routing decisions. For example, the underwater sensors in learn the location and speed of mobile beacons and neighbors during the localization phase; the position and motion of mobile beacons are used by the routing protocol to choose the best relay for a node to forward its data. Localization approaches proposed for ground-based sensor networks do not work well underwater because long propagation delays,Doppler effect, multipath, and fading cause variations in the acoustic channel. Bandwidth limitations, node mobility, and sparse deployment of underwater nodes also affect localization estimation. Proposed terrestrial localization schemes based on received signal strength (RSS) are not recommended in UWCNs, since non-uniform acoustic signal propagation causes significant variations in the RSS. Time of arrival (ToA) and time difference of arrival (TDoA) measurements require very accurate time synchronization (which is a challenging issue), and angle of arrival (AoA) algorithms are affected by the Doppler shift. Localization schemes can be classified into:
Range-based schemes (using range and/or bearing information): The location of nodes in the network is estimated through precise distance or angle measurements.
Anchor-based schemes: Anchor nodes are deployed at the seabed or sea surface at locations determined by GPS. The propagation delay of sound signals between the sensor or AUV and the anchors is used to compute the distance to multiple anchor nodes.
Distributed positioning schemes: Positioning infrastructure is not available, and nodes communicate only with one-hop neighbors and compute their locations using multilateration. Underwater sensor positioning (USP) has been proposed in as a distributed localization scheme for sparse 3D networks, transforming the 3D underwater positioning problem into a 2D problem using a distributed non-degenerative projection technique. Using sensor depth information, the neighboring reference nodes are mapped to the horizontal plane containing the sensor to be localized. After projecting thereference nodes, localization methods for 2D networks such as bilateration or trilateration can be used to locate the sensor.
Schemes that use mobile beacons/anchors:They use mobile beacons whose locations are always known. Scalable localization with mobility prediction (SLMP) has been proposed in [15] as a hierarchical localization scheme. At the beginning, only surface nodes know their locations,and anchor nodes can be localized by these surface buoys. Anchor nodes are selected as reference nodes because of their known locations; with the advance of the location process more ordinary nodes are localized and become reference nodes. During this process, every node predicts its future mobility pattern according to its past known location information. The future location is estimated based on this prediction.
Range-free schemes (not using range or bearing information): They have been designed as simple schemes to compute only coarse position estimates. A range-free scheme proposed in [16]estimates the location of a sensor within a certain area.None of the aforementioned localization schemes was designed with security in mind. Some localization-specific attacks (replay attack, Sybil attack, wormhole attack) have previously been described.Open research issues for secure localization are:
- Effective cryptographic primitives against injecting false localization information in UWCNs need to be developed.
- It is necessary to design resilient algorithms able to determine the location of sensors even in the presence of Sybil and wormhole attacks.
- Techniques to identify malicious or compromised anchor nodes and to avoid false detection of these nodes are required.
- Secure localization mechanisms able to handle node mobility in UWCNs need to be devised.
5.3 SECURE ROUTING
Routing is essential for packet delivery in UWCNs. For example, the Distributed Underwater Clustering Scheme (DUCS) does not use flooding and minimizes the proactive routing message exchange. Routing is specially challenging in UWCNs due to the large propagation delays, the low bandwidth, the difficulty of battery refills of underwater sensors, and the dynamic topologies.Therefore, routing protocols should be designed to be energy-aware, robust, scalable and adaptive.Many routing protocols have been proposed for underwater wireless sensor networks. However,none of them has been designed with security as a goal. Routing attacks can disable the entire networks operation. Spoofing, altering,or replaying routing information affects routing. Important routing attacks (selective forwarding, sinkhole attack, Sybil attack, wormhole attack, HELLO flood attack, acknowledgment spoofing) have been previously described.Although the attacks against routing in UWCNs are the same as in ground-based sensor networks,the same countermeasures are not directly applicable to UWCNs due to their difference in characteristics. Proposed broadcast authentication methods would cause high communication overhead and latency in UWCNs. Multipath routing would cause high communication overhead as well.
Open research issues for secure routing are:
There is a need to develop reputation-based schemes that analyze the behavior of neighbors and reject routing paths containing selfish nodes that do not cooperate in routing. The proper functioning of these schemes is challenging because they do not work well in mobile environments,the time required to detect compromised nodes increases substantially in UWCNs due to the long propagation delays, and they must be adapted to tolerate short-term disruptions.
Quick and powerful encryption and authentication mechanisms against outside intruders should be devised for UWCNs because the time required for intruder detection is high due to the long and variable propagation delays, and routing paths containing undetected malicious nodes can be selected in the meantime for packet forwarding.
Sophisticated mechanisms should be developed against insider attacks such as selective forwarding,Sybil attacks, HELLO flood attacks,and acknowledgment spoofing.
There is a need to develop new techniques against sinkholes and wormholes, and improve existing ones. With Dis-VoW a wormhole attack can still be concealed by manipulating the buffering times of distance estimation packets.The wormhole-resilient neighbour discovery in is affected by the orientation error between sensors.
6. CONCLUSION
In this article we have discussed security in UWCNs, underlining the specific characteristics of these networks, possible attacks, and countermeasures. The main research challenges related to secure time synchronization, localization, and routing have also been surveyed. These research issues remain wide open for future investigation.
sir give reference for securing under water wireless communication network
Hello sir, this s bhuvi can u send me more topics in wireless communicaiton network
Hi,
Wireless Computer Communications Using Sound Waves
https://krazytech.com/technical-papers/securing-underwater-wireless-communication-networks
Ad-hoc Wireless Networks
Capturing packets in secured networks
Challenges in mobile ad hoc networks (manets)
Securing underwater wireless communication networks
Security requirements in wireless sensor networks
Wireless integrated network sensors
Comments are closed.